NETWORK SECURITY
True Network Security Starts From Within
 It seems like we hear stories on yet another security breach every day. OPM is the biggest one lately, and there might even be another ‘big’ breach by the time I’m finished writing this post. One of my favorites recently was the Astros ‘hack’. The St. Louis Cardinals had been illegally accessing the Houston Astros’ private networks. The hackers have been identified as a group of Cardinal employees; No one would have pegged this group as the stereotypical “hackers.”
It seems like we hear stories on yet another security breach every day. OPM is the biggest one lately, and there might even be another ‘big’ breach by the time I’m finished writing this post. One of my favorites recently was the Astros ‘hack’. The St. Louis Cardinals had been illegally accessing the Houston Astros’ private networks. The hackers have been identified as a group of Cardinal employees; No one would have pegged this group as the stereotypical “hackers.”
In March of 2014, cybercriminals used a Sally Beauty Supply district manager’s username and password to log in to the company’s secure network and steal the payment information of approximately 25,000 customers. Just over one year later, Sally suffered yet another data breach. The similarity? Both breaches were the result of Sally’s own employee’s negligence.
Sally Beauty Supply is not the first – and certainly not last – company to suffer a breach at the hands of their own members. In fact, more than 52 percent of corporate data breaches are the result of human error, according to a recent CompTIA survey.
Security education for employees takes time and effort, but is well worth the investment if it means avoiding a costly and damaging data breach. Here’s why:
Why Security Training is Important
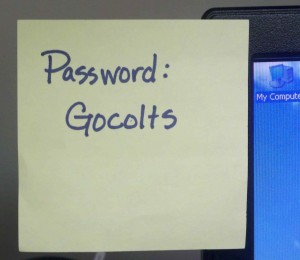
While most people don’t post their login on a sticky note (like the district manager mentioned above), employees still often do not take the appropriate measures to secure their company’s information. Because they don’t know what to look for, employees are falling for social engineering schemes and inadvertently granting entry into the network.
The most common of these social engineering schemes are phishing emails and websites, which contact the user and claim that they may need to “confirm their identity” by submitting private information. A similar type of threat, called spear phishing, is an even more targeted version of phishing where emails and websites are personalized –sometimes to extreme degrees – to grab the attention of the victim. When a workforce is (hopefully) busy working, these may seem like innocuous, unsuspicious items that may sneak through the cracks and into the system.
Helping a workforce understand the importance of strong passwords and how to spot common phishing attacks is easier said than done. Here are some simple tips for preparing a workforce to keep company data secure.
Keep it Simple
IT Pros live and breathe the technology that they work with everyday. However, that is not always the case with their coworkers. Though the IT manager may be able to speak to phishing attacks or network breaches on a very high level, it is crucial that the information is discussed in simple, digestible terms.
Be sure to encourage questions from trainees. Stop at intervals to ask specific individuals questions regarding the content in order to reassure that everyone is on the same page. Above all, stress the importance of the role each employee plays in keeping the company’s information safe from criminals – no one is immune.
Stay Informed
Make sure each employee is aware of threat patterns, trends, and news by sharing information in a newsletter or sending a company-wide email as it happens. If they are already aware of a potential threat coming their way, they’ll be wary of the suspicious emails they’ve been told to look out for.
Practice Often
Every workforce should actively practice knowledge of potential threats. A simple quarterly security quiz will allow managers to pinpoint who may need a little more time learning about how they play a role in data security. As the saying goes, a chain is only as strong as its weakest link. Testing your employees on their ability to avoid social engineering schemes is crucial to knowing how strong your chain is.
Defend from Within
Security software can’t catch a perp when the perp uses legitimate means, like employee logins, to access a company’s network. An organization can integrate every available network security tool and still suffer a data breach. But when a company is strong on the inside, that’s just one more layer of security that helps protect a company’s private and sensitive data.
Put Us In Your Corner.
We back you up with managed threat protection, visibility, and support, 24/7.