NETWORK SECURITY
Limit The Damage Of Ransomware In Two Steps
 Unless you make it a habit of reading blogs about bitcoin or spend your spare time on sites dedicated to network security then you may have missed the announcement last week by the FBI on ransomware.
Unless you make it a habit of reading blogs about bitcoin or spend your spare time on sites dedicated to network security then you may have missed the announcement last week by the FBI on ransomware.
OK, to be fair, it wasn’t an official announcement, just a comment from one of the FBI’s leaders in cybersecurity during a recent summit. Essentially, what Joseph Bonavolonta, the Assistant Special Agent in Charge of Cybersecurty and Counter Intelligence in the FBI’s Boston office, told the crowd at the Cyber Security Summit 2015 was that if you happened to be hit with Cryptolocker, Cryptowall, or one of the other variants of ransomware then your network may be beyond help.
“The ransomware is that good,” Bonavolonta said. “To be honest, we often advise people just to pay the ransom.”
Fill out the form below for a free evaluation.
Defending Yourself Against Ransomware
Sounds like a defeatist attitude, for sure. But, ransomware has been evolving. While Cryptolocker may be old news, its variants aren’t. Malware like Cryptowall is still out there infecting networks and doing a great job of making data inaccessible.
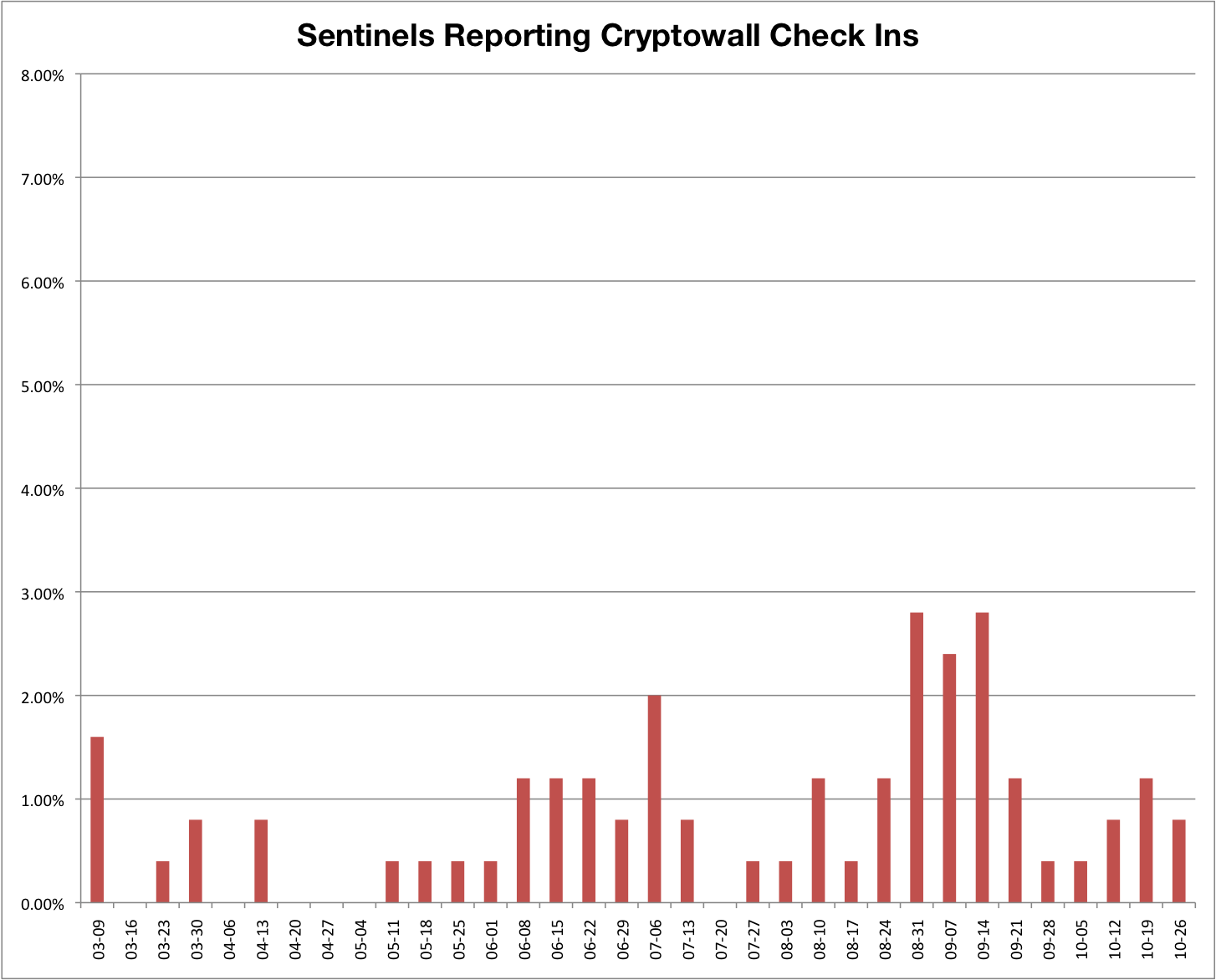
For example, our own CINS data – alert data pulled from our Sentinels installed around the world – seems to corroborate a resurgence of Cryptowall beginning earlier this year, and continuing with a steady stream of infections. The chart below shows a slow, steady drip of Cryptowall check ins caught by our customers’ Sentinels since March 2015.
So how do you limit the effectiveness of ransomware? There are two things that you need to do.
Create Regular Backups
The one thing that often forces the hand of someone infected with ransomware is that they don’t have regular backups. They can’t go get a recent copy of the data that the hackers have encrypted.
We heard a story at a recent event of a small town sheriff who had his network infected by ransomware. The hackers had locked him out of his network and 13 years of data that wasn’t backed up. He had no choice; he had to pay the ransom, and hope he’d actually get his data back. (Luckily, he did.)
That’s what having a regularly backed up network can help you avoid. How regular the back up needs to be will depend on the network and the data that’s on it, but just having a point in time that you can restore to takes some of the power out of the hands of the hackers.
Also, unless you are running off of shared servers (with good back ups), you will probably want to set up backups for the network endpoints as well.
Keep your IPS Rulesets Up To Date and Use Threat Intelligence
The second thing you can do to protect yourself from Cryptolocker and all of its variants and copycats is to utilize your IPS and use threat intelligence to block the IP addresses known to be distributors of this stuff.
Any decent IPS will have solid rules that look specifically for known ransomwares’ initial outbound communications – assuming the rulesets are kept current, and someone is monitoring the IPS alerts.
And as for threat intelligence, the data is out there. You can either go out and gather it yourself, then enter the bad IP addresses into your network’s IPS or firewall, or you can use a managed IPS solution and have it automatically updated for you. For example, in the past, the blog at cisecurity.org has been helpful in providing an up-to-date list of IPs for Cryptolocker C2 servers.
Either way, keeping those IP addresses from accessing your network can go a long way to keeping your data out of the hands of hackers.
Free 14-Day Trial
Network Gateway Assessment
We will use this information to contact you about the 14-Day Trial. We do not share or sell this information to anyone. See our Privacy Policy for more.
Put Us In Your Corner.
We back you up with managed threat protection, visibility, and support, 24/7.